1 Introduction
The current management process of radio-electronic signal blocking systems faces several challenges. One of the most significant problems is inefficiency in signal blocking, resulting in failures of the blocking system and the occurrence of unauthorized calls from within penal institutions.
Moreover, compliance with the allowed signal levels inside the prisons as per the current regulations is not achieved, leading to frequent requests to the authorities to conduct radiofrequency signal measurements in the untouchable zone and to verify compliance with these standards.
Another critical aspect is the generation of social conflicts in communities near the prisons due to the negative impact of the blocking systems on public telecommunications services. Blocking techniques must impact the quality parameters of the signal. For example, in the case of LTE, according to the research conducted by Mahendra, Budiman, Cahyadi, and Taruk [1], blocking techniques can affect measures such as Reference Signal Received Power (RSRP), Reference Signal Received Quality (RSRQ), and Signal to Noise Ratio (SNR).
Regarding the blocking techniques themselves, Samir and Shaheen [2] mention several models of blocking signals, including Barrage, Band Jamming (BJ), Partial Band Noise Jamming (PBJ), Pulsed Jamming Technique, and a combination of the last two called Partial-Pulsed Band jamming (PPBJ).
Jasim and Kamil [3] also highlight different techniques of Jamming attacks, such as Direct Jamming, Flooding Jamming, Selective Jamming, and Denial of Service (DoS) Jamming. Concerning the goal of jamming attacks, Mert and Gunes [4] suggest that for LTE, targeting the main synchronization signals (primary and secondary, PSS and SSS) in the Downlink is an effective strategy.
On the other hand, El-Keji, Ureten, Yanikomeroglu, and Yensen [5] indicate that LTE is vulnerable to jamming and that the most susceptible control channel in the Downlink is the Physical Downlink Control Channel (PDCCH). These findings underscore the importance of understanding and mitigating jamming threats in LTE networks. Different approaches have been discussed regarding interference in LTE systems. Bazzo, Takaki, Barros, and Carrillo [6] suggest that mitigation techniques are available for both Downlink and Uplink in the LTE system.
However, Mohamed Elatif Soliman [7] raises that partial band interference may be more effective than the barrier interference technique. It is also highlighted that the most effective location for the interference signal is at the center of the six RB (resource blocks) where the synchronization channels (PSS and SSS) and PBCH are located.
On the other hand, Eduard Krutisky [8] emphasizes that launching an interference attack can be easier than mitigating it, although it is possible to develop countermeasures, but these do not guarantee complete protection of all networks.
Ali, Baddeley, Bariash, Lopez, Lunardi, and Giacalone [9] conducted an analysis of the error rate performance in WLAN IEEE 802.11n communication systems in the presence of different types of interferences.
The aforementioned studies present various approaches to the vulnerability of LTE to jamming attacks. Vo-Huu, Vo-Huu, and Noubir [10] highlight an interference strategy that can have a significant impact, destroying more than 95% of the transmitted packets with only 0.1% of the regular transmitted signal power.
Marc Lichtman, Roger Piqueras, Mi.na Labib, Vuk Marojevic, and Jeffrey Reed [11] point out that LTE is vulnerable to jamming attacks because it was not originally designed to be a critical communications technology. Conversely, Rafal Krenz and Soumya Brahma [12] warn about the vulnerability of LTE to be jamming attacks and denial of service (DOS) attacks, which can effectively disrupt communication.
Vuk Marojevic, Jeffrey Reed, and Raghunandan Rao [13] highlight the threat posed by jamming attacks on the PSS/SSS channels to the performance of LTE after a device connects to a cellular base station (EBC). In addition, Ibrahim Patel, Ashok Shigli, and Srioathi Raja [14] managed to successfully experiment with jamming to inhibit phone calls.
Hossein Pirayesh and Huacheng Zeng [15] investigated jamming attacks on Wi-Fi and mobile networks, analyzing their PHY and MAC layers, and explored possible countermeasures, also addressing the vulnerability of LTE to jamming attacks, evaluating their PHY and MAC layers, and considering security measures. The study conducted by Yulong Zou, Jia Zhu, Xianbin Wang, and Lajos Hanzo [16] highlights the vulnerability of radiofrequency (RF) transmissions to jamming attacks. This is due to the nature of radio propagation, which can be susceptible to external interference, in addition, security at the physical layer of wireless communications can be compromised by effective jamming attacks. According to Victor Gil Jimenez, Ana Garcia Amada, and Francisco Hernando Gallego [17], orthogonal sequences have been developed to interfere with UMTS transmission signals, reducing the energy required to carry out a jamming attack.
Furthermore, Grecia Romero, Virginie Deniau, and Olivier Stienne [18] observe that the error rate in jamming attacks on Wi-Fi signals with protocol 802.11n can vary according to the waveform of the interference signal. Regarding the 5G NR (Fifth Generation) technology, Marc Lichtman, Vuk Marojevic, and Jeffrey Reed [19] note that it is less vulnerable to interference compared to LTE, due to its dynamic nature and the elimination of dispersed control channels.
However, Youness and Saleh [20] mention that 5G NR still uses primary and secondary synchronization signals (PSS and SSS), and Skokowski, Kelner, Malon, Maslanka, Birutis, Vasquez, Saha, Low, Czapiewska, Magiera, Rajchowski, and Ambroziak [21] assert that an effective jamming attack on 5G NR targets these synchronization signals, the physical broadcast channel (PBCH), and the downlink control channel (PDCCH) at the physical layer (PHY).
It is public knowledge that complaints persist about the making of unauthorized telephone calls from within different penal establishments. Therefore, it is essential to improve the efficiency indicators of the radio-electric signal blocking. Moreover, the Ministry of Transport and Communications (MTC) has conducted numerous radiofrequency (RF) signal measurements because both the service provider and mobile operators do not comply with the signal level limits established by legal regulations.
This highlights the need to establish more agile coordination lines for the regulation of these aspects. This has become even more pronounced during the pandemic era when classes and work were conducted virtually. The goal of implementing Best Practices is to optimize the Management of the Radio-Electric Signal Blocking System in Penal Establishments, using the FRS methodology.
The article is structured as follows: section 2 presents the Theoretical Background, where a synthesis of the relevant theory is offered. Section 3 addresses the Research Method used. The development of the new Collaborative Model SKX and its phases are presented in section 4. Section 5 is dedicated to the Case Study conducted in Peru. In section 6, the Results are presented and discussed in detail. Finally, section 7 presents the Conclusions and outlines areas for future research.
2 Theoretical Background
This section provides a solid and essential context for understanding the implementation of Best Practices in the Management of Radio-Electronic Signal Blocking Systems at the Ministry of Justice in Peru. It explores historical and conceptual backgrounds related to signal blocking technology.
2.1 Best Practices
In the context of managing radio-electronic signal blocking systems, it has been deemed best practice to block or jam signals on the Downlink. This includes synchronization signals PSS, SSS, the physical broadcast signal (PBCH), and the control channel (PDCCH), in that order of priority, according to various studies by Nieves and Wyglinski [22], Youness and Saleh [20], among others. In addition, it has been determined that the jamming signal should be centered on the carrier. Regarding best practices related to the prison environment, the publication GSMA Latin American [23] has identified the following recommendations: identifying the penitentiary establishments that truly require a radio-electronic signal blocking system, analyzing and defining the technical solution for each prison, taking into account its individual characteristics and needs, coordinating with radio spectrum authorities and mobile operators to define signal levels, and carrying out controlled tests.
2.2 Management of Radio-Electronic Signal Blocking Systems
Pavel Tomasek [24] has conducted a study in this regard, verifying that these arrangements cannot block magnetic fields, such as the Earth's magnetic field, but can protect the interior from electromagnetic radiation coming from outside. Farhan Aziz, Jeff Shamma, and Gordon Stuber [25] proposed an algorithm to estimate the type of interference with high probability and rapid convergence. Hadeel Obaid [26] pointed out that pulsed jammers can degrade network performance and cause a denial of service. Hossein Noori and Saeed Sadeghi [27] explored anti-jamming measures in two different scenarios, one where the target user has a lot of power and can block other users, and another where the target user has little power and does not affect the transmissions of others.
Birutis and Mykkeltveit [28] suggest that the most effective method to block the Downlink in 5G is to use Barrage Jamming (BJ) with high power in EIRP (Equivalent Isotropically Radiated Power), compared to blocking the synchronization signals (PSS and SSS). Regarding the deployment of 5G technology, Agiwal, Kwon, Park, and Hin [29] mention that the 3GPP standard allows dual connectivity using both 4G LTE and 5G NR at the same time.
This means that if an operator uses an LTE network infrastructure composed of the EPC core and LTE base stations (eNB), it can implement dual connectivity for the initial commercialization of 5G networks.
In this context, Fehmi, Fakhouri, Bahnasse, and Talea [30] explain that 5G NSA (Non-Standalone) is deployed in areas where there is already an existing LTE core and LTE radio access network (EPC).
3 Research Method
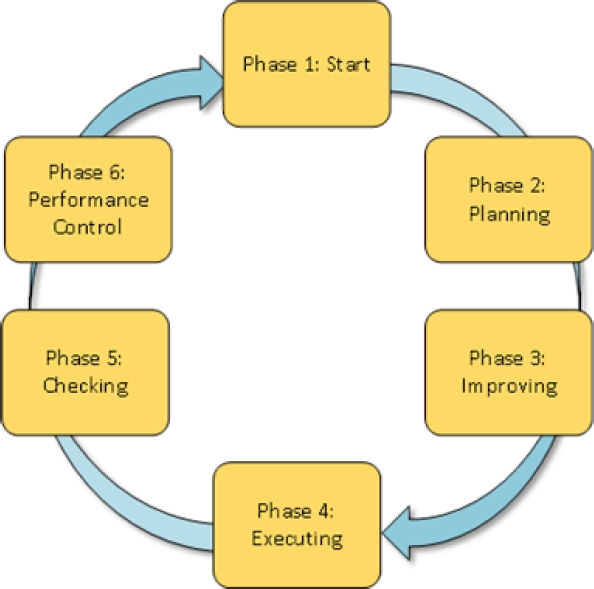
This section details the innovative experimental methodology used to assess the influence of radio-electronic interferences on various communication technologies. It also describes the phases of the Scientific Method adopted for its implementation and empirical validation. Collaborative Meta-Model: Agile FRS Methodology. The FRS Methodology represents an innovative approach designed to improve the current process of managing blocking systems in penal institutions. It comprises six key phases with the goal of contributing new knowledge and criteria to reduce the impacts caused by these systems in the surrounding areas of prisons (See Figure 1). The phases of the new agile FRS methodology are:
Phase 1. Initiation, involves the process associated with the signing of the Unnamed Service Provision Contract "Provision of Technological Security Services in Prisons" (CIPS), for the provision of public fixed telephone service inside thirty-three (33) Penal Establishments (EP), receiving the service of blocking and/or inhibition of radio-electronic signals in the EPs, for 25 years. The deliverable in this phase is the signing of the Contract and the responsibilities assumed.
Phase 2. Planning, during this phase, specialized technical studies are carried out to assess the technical infrastructure that will be installed in each of the penal establishments.
Additionally, it includes the acceptance process by specialized personnel, who verify the mentioned studies.
Phase 3. Improvement, studies designed to significantly mitigate or prevent the blocking system equipment from generating negative interferences in the surroundings of the prisons will be carried out.
Phase 4. Execution, proceeds with the installation of all the technological infrastructure in the penal establishments, as described in the specialized technical studies. This includes the implementation of recommendations arising from studies of non-affectation to the population and interference with mobile operators. Likewise, exhaustive tests of the entire system are carried out, and the necessary verifications are made to ensure its correct operation.
Phase 5. Verification, Specialized personnel carry out exhaustive evaluations to determine if the blocking system affects public telecommunications services in the untouchable zone and if it causes interference with mobile operators. In case the results of these evaluations are favorable, and no significant negative impacts are detected.
Phase 6. Monitoring and Control, Throughout the operation period, from the beginning to the end of the contract, the blocking systems will be in full operation and will be subject to constant monitoring. Specialized personnel will carry out the monitoring and control of these systems within the penal establishments, while also evaluating any possible impact on public telecommunications services outside the prisons.
3.1 Applied Research Method
3.1.1 Operationalization of Variables
Table 1 shows the operationalization of the dependent variable.
Table 1 Operationalization of the Dependent Variable: Management of Radio-Electronic Signal Blocking Systems
| Indicator | Index | Unit of Measure | Observation Unit |
| Number of events or complaints of failures in the blocking of the EPs | [1-24] | Events | Reports, indirect observation |
| Number of requests to the MTC to perform measurements | [1-24] | Requests | Reports, indirect observation |
| Number of social protests in the vicinity of the EP | [1-24] | Protests | Reports, indirect observation |
3.1.2 Research Design
The research is classified under the experimental design focusing on the category of "pure" experiments. It involves a comparison of the experimental group (Ge) composed of randomly selected (R) Management Processes of Radio-Electronic Signal Blocking Systems, from which values O1 are obtained. After that, the stimulus (X), the Best Practices according to the FRS methodology, is provided, and post-test results without the stimulus to the control group (Gc), O2, are expected:
3.1.3 Universe and Sample
The study universe comprises all the Management Processes of Radio-Electronic Signal Blocking Systems operating within penal establishments in Peru, with an indeterminate size
3.1.4 Data Collection Procedure
Throughout the study, indirect observation methods were employed, and specialized databases were consulted. The collected data were analyzed using Minitab statistical software, with descriptive statistics applied to characterize each studied indicator. Additionally, for the scrutiny of the relationship between variables and the verification of hypotheses, inferential statistics techniques were used, employing the Student's t-test for the analysis of parametric nature indicators.
3.1.5 Hypothesis Statement
H1: If Best Practices are applied using the FRS methodology, it is expected that the number of events or complaints related to blocking failures will decrease, which would translate into an increase in the efficiency of the Management of the Radio-Electronic Signal Blocking System in Penal Establishments.
H2: If Best Practices are applied using the FRS methodology, it is expected that the number of requests to the MTC to perform signal measurements to detect signal levels above what is allowed will decrease in areas close to where the Radio-Electronic Signal Blocking System is installed in Penal Establishments.
H3: If Best Practices are applied using the FRS methodology, it is expected that the number of social protests in populations near the prisons, where the Radio-Electronic Signal Blocking Systems are installed in Penitentiary Establishments, will decrease.
For the contrast of the hypotheses, the following solution was proposed for each of the indicators:
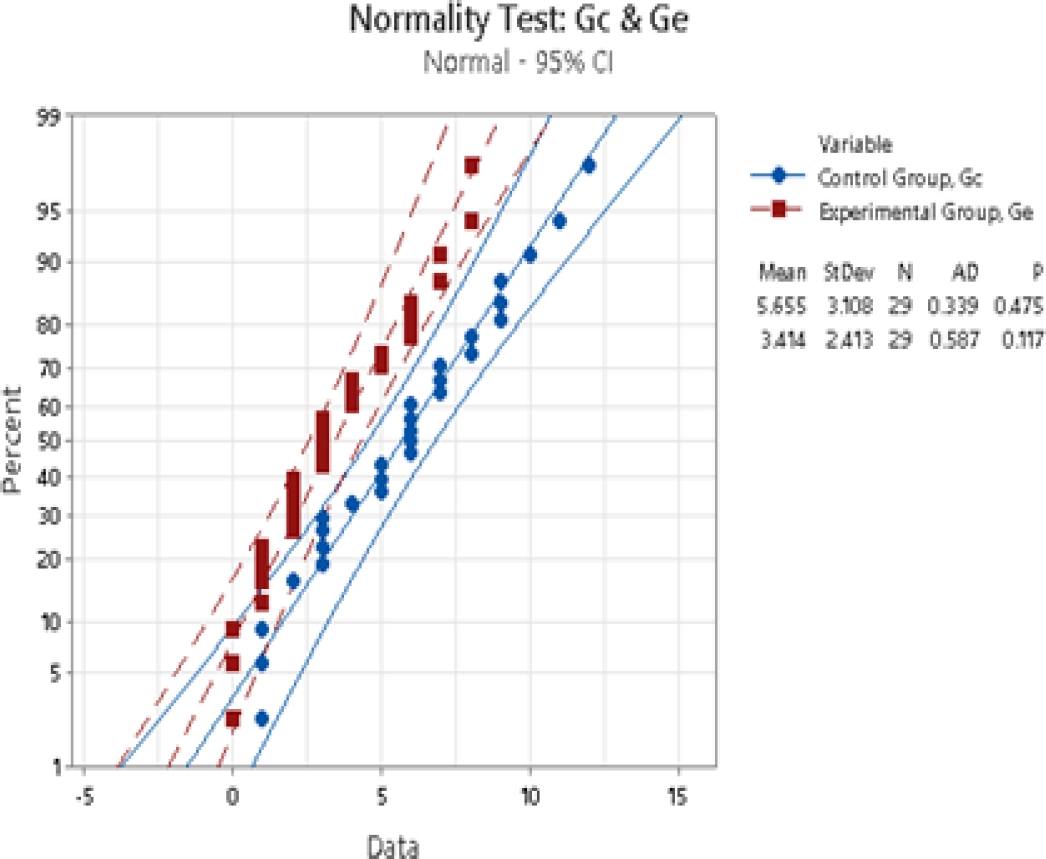
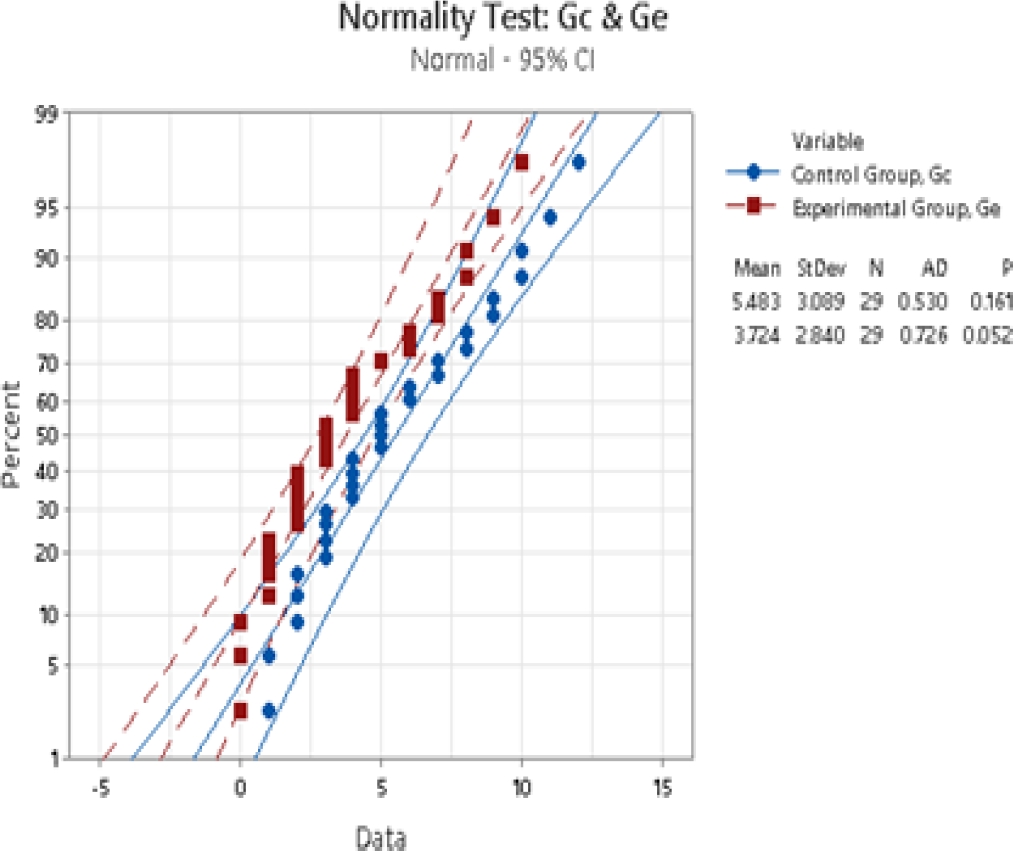
where: Ho: μ1 ≤ μ2, Ha: μ1 > μ2. Finally, the normality test of data, descriptive statistical analysis (See Figure 15, Figure 16, Figure 17, Table 3, and Table 4), and hypotheses were validated using the Student's t-test with the specialized software Minitab (See Table 5).
Table 2 Frequencies of blockers
| Band | Jamming Range (MHz) |
| 700 MHz | 758-803 |
| 850 MHz | 851–894 |
| 900 MHz | 939–960 |
| 1900 MHz | 1930–1990 |
| 2100 MHz | 2110–2150 |
| 2300 MHz | 2360–2390 |
| 2.4 GHz [Wi-Fi] | 2400–2483.5 |
| 2600 MHz | 2570–2615 TDD |
| 2615–2690 FDD | |
| 3500 MHz | 3500–3600 TDD |
| 5 GHz [Wi-Fi] | 5150–5850 |
| 1500 MHz | 1520–1570 / 1610-1675 |
Table 3 Results with Descriptive Statistics
| Sample | n | Mean | StDev | AD | p-value |
| I1: Post-Test (Gc) | 29 | 4.66 | 2.73 | 0.465 | 0.237 |
| I1: Post-Test (Ge) | 3.48 | 2.35 | 0.632 | 0.09 | |
| I2: Post-Test (Gc) | 29 | 5.66 | 3.11 | 0.339 | 0.475 |
| I2: Post-Test (Ge) | 3.41 | 2.41 | 0.587 | 0.117 | |
| I3: Post-Test (Gc) | 29 | 5.48 | 3.09 | 0.53 | 0.161 |
| I3: Post-Test (Ge) | 3.72 | 2.84 | 0.726 | 0.052 |
Table 4 Summary of Results for the Indicators
| Sample | n | 95% CI for Mean | |
| I1: Post-Test (Ge) | 29 | 2.587 – 4.378 | |
| I2: Post-Test (Ge) | 29 | 2.496 – 4.331 | |
| I3: Post-Test (Ge) | 29 | 2.644 – 4.804 | |
| Sample | Kurtosis | Skewness | Q3 |
| I1: Post-Test (Ge) | -1.0087 | 0.287 | 6 |
| I2: Post-Test (Ge) | -0.8357 | 0.4247 | 5.5 |
| I3: Post-Test (Ge) | -0.5435 | 0.642 | 6 |
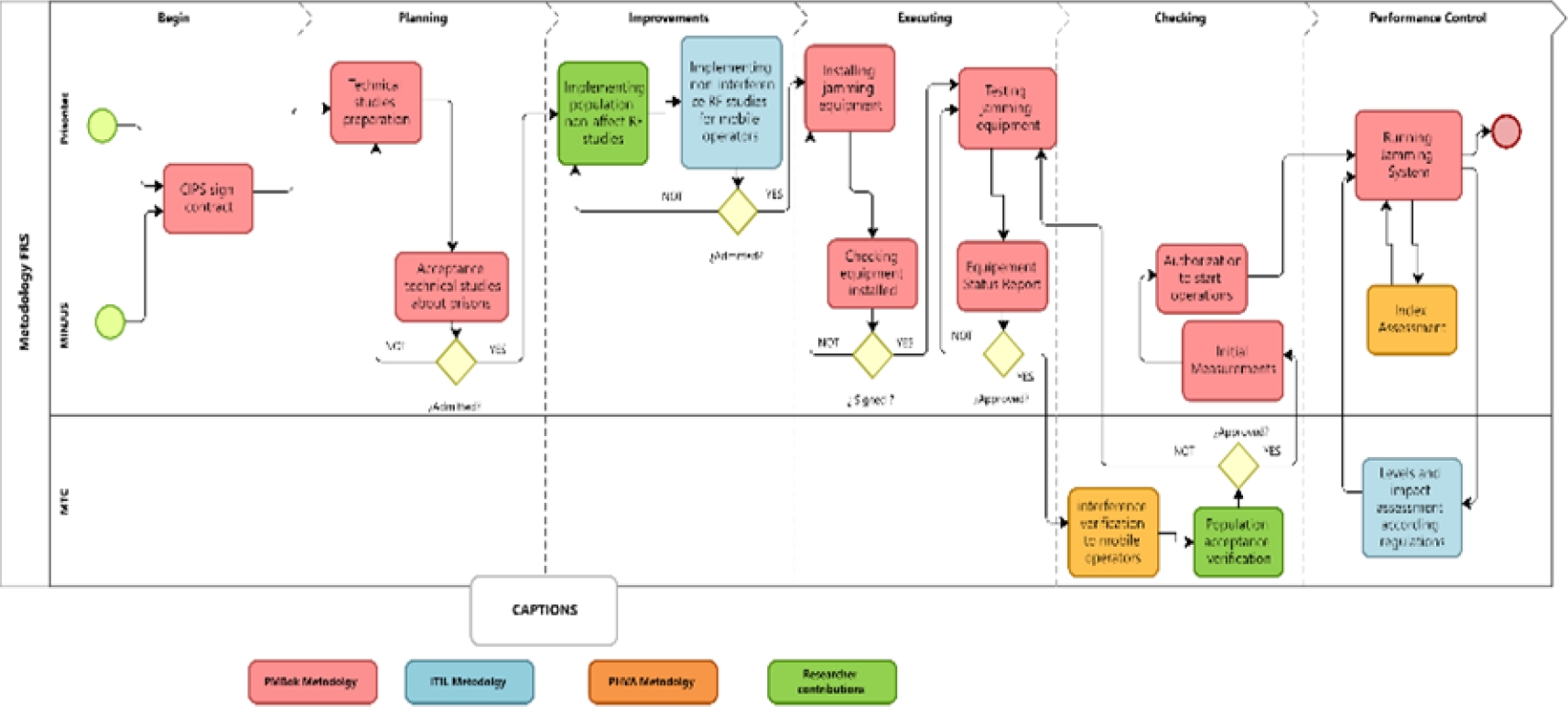
3.1.6 Development of the New Collaborative FRM Model
Next, the methods used to develop the new FRM methodology for the Management of radio-electronic signal blocking systems in penal facilities are presented.
3.1.7.1 Project Management Methodology based on PMBok
Project Management involves the strategic implementation of knowledge, skills, tools, and methodologies on project tasks to meet the stipulated requirements [31]. This process manages tasks with established schedules and concrete goals, as illustrated in Figure 2.
Phase 1. Initiation Processes: According to the authors [31], at this stage, the organization establishes the project's objectives, identifies the main stakeholders, appoints the Project Manager (PM), and grants formal authorization to initiate the project [32].
Phase 2. Planning Processes: [31] state that stakeholders play a crucial role in defining the project's scope and setting its objectives. At this stage, the work team develops a plan that will serve as a guide to achieve project success.The planning processes follow an integral approach, ensuring detailed planning before starting the project execution to produce the final product [32].
Phase 3. Execution Processes: [31] indicate that the project manager plays a key role in coordinating all the necessary resources to launch the project management plan.
This is where the project work is executed, using most of the allocated resources, time, and budget to achieve the project's objectives and the estimated business value [32].
Phase 4. Monitoring and Control Processes: [31] affirm that the project manager and their team are continuously monitoring the project's progress and taking corrective actions when necessary.
This stage focuses on evaluating real and quantitative data on how the project is developing compared to the original plan and determining the measures to address any variation that exceeds acceptable limits [32].
Phase 5. Closing Processes: [31] mention that the client formally accepts the project deliverables, which is essential since all projects must have a formal closure, regardless of whether they have been completed or not. The project closing processes involve administrative activities, such as collecting and finalizing all the necessary documentation to complete the project [32].
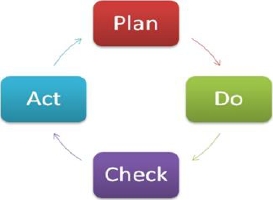
3.1.7.2 PDCA Cycle (Plan, Do, Check, Act)
Also known as Deming's Cycle, it consists of four phases: Plan, Do, Check, Act, as shown in Figure 3.
− Phase 1. Plan: Where the system's objectives and processes are established, as well as identifying and allocating the necessary resources to generate the desired outcomes [33].
− Phase 2. Do: Where tasks are executed and implemented as planned in Phase 1.
− Phase 3. Check: Essential for carrying out the monitoring and measurement of the processes and the resulting products and services compared to what was planned [33].
− Phase 4. Act: In this phase, it is crucial to take actions to improve performance and leverage opportunities for improvement. Actions necessary to correct unwanted effects and ensure that the project progresses as planned should also be implemented [33].
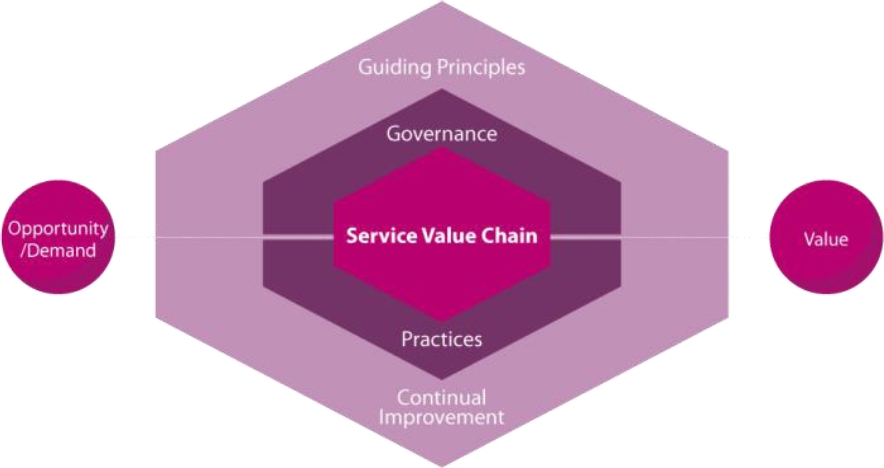
3.1.7.3 ITIL Methodology
Provides a comprehensive digital operational model covering the entire organizational spectrum from start to finish, efficiently managing the provision and operation of IT-powered products and services [34], as detailed in Figure 4.
− Phase 1, Plan: Ensures that all involved parties have a common understanding of the vision, the current situation, and the direction towards improvement in the four dimensions [34].
− Phase 2, Improve: Promotes the constant improvement of products, services, and practices at all stages of the organization's value chain [34].
− Phase 3, Engage: Encourages a solid understanding of stakeholder needs, promotes transparency, and maintains ongoing commitment [34].
− Phase 4, Design and Transition: Ensures that products and services meet the stakeholders' quality expectations, costs, and market times [34].
− Phase 5, Obtain and Build: Ensures that service components are available at the required time and place [34].
− Phase 6, Deliver and Support: Ensures that services are delivered and supported according to the agreed specifications [34].
3.1.8 Collaborative Meta-Model: FRM Methodology
After thorough analysis of existing models, an innovative model has been developed, whose flowchart is presented in Figure 5.
4 Case Study
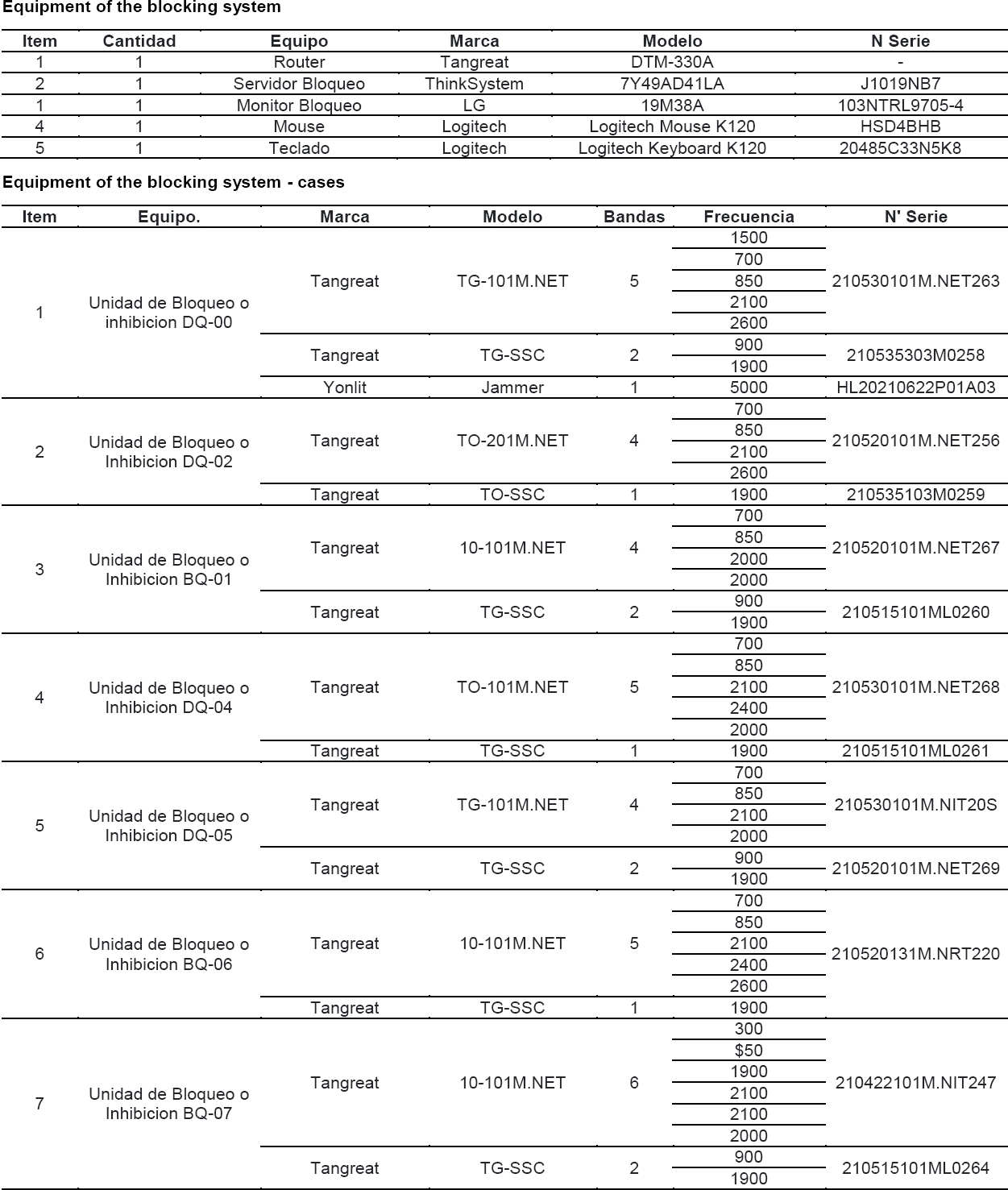
The FRS methodology presents a proposal aimed at improving the current method used in the installation of Blocking or Inhibition Systems in penal establishments.
4.1 Phase 1: Initiation
Involves the process associated with the signing of the Unnamed Service Provision Contract "Technological Security Services in Prisons" (CIPS), for the provision of fixed public telephone service inside 33 Penal Establishments (EP), receiving the service of blocking and/or inhibition of radio-electronic signals in the mentioned EPs, for 25 years. The deliverable in this phase isthe signing of the Contract and the responsibilities assumed.
4.2 Phase 2: Planning
The Provider is responsible for carrying out technical studies related to all the technological infrastructure that will be installed in the penal establishments. These studies cover fundamental aspects, such as the blocking system itself, including equipment, transmitters, antennas, and support structures.
They also encompass the power system, which includes electrical wiring, the generator set, and the electrical distribution, as well as the communications room and the conduit needed for electrical and telecommunications wiring. This document, called Specialized Technical Studies (ETE), is one of the main deliverables of this phase and is sent to MINJUS for review and, if applicable, approval.
4.3 Phase 3: Improvement
Studies specifically designed to significantly mitigate or completely avoid the blocking system equipment from generating negative interferences in the surroundings of the prisons will be carried out.
This includes both public telecommunications services and the prevention of interference in mobile operators' base stations, that is, without causing inconvenience or negatively affecting the surrounding telecommunications networks.
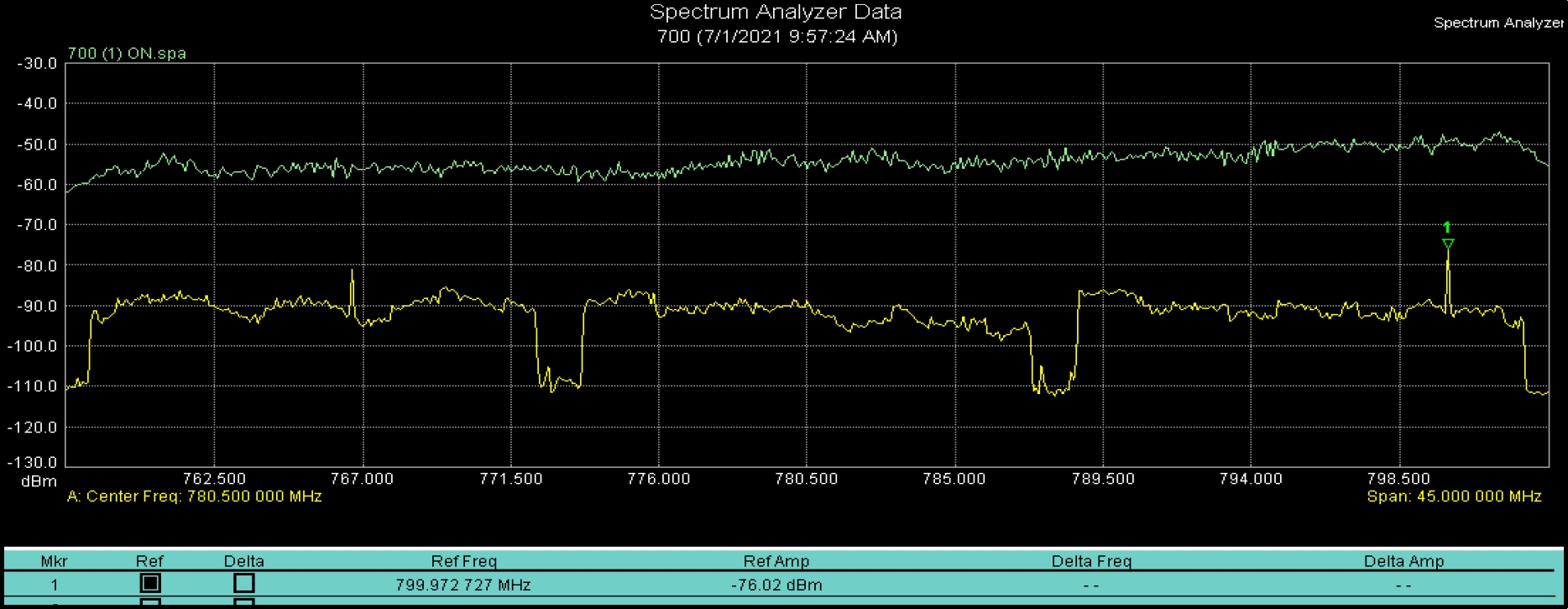
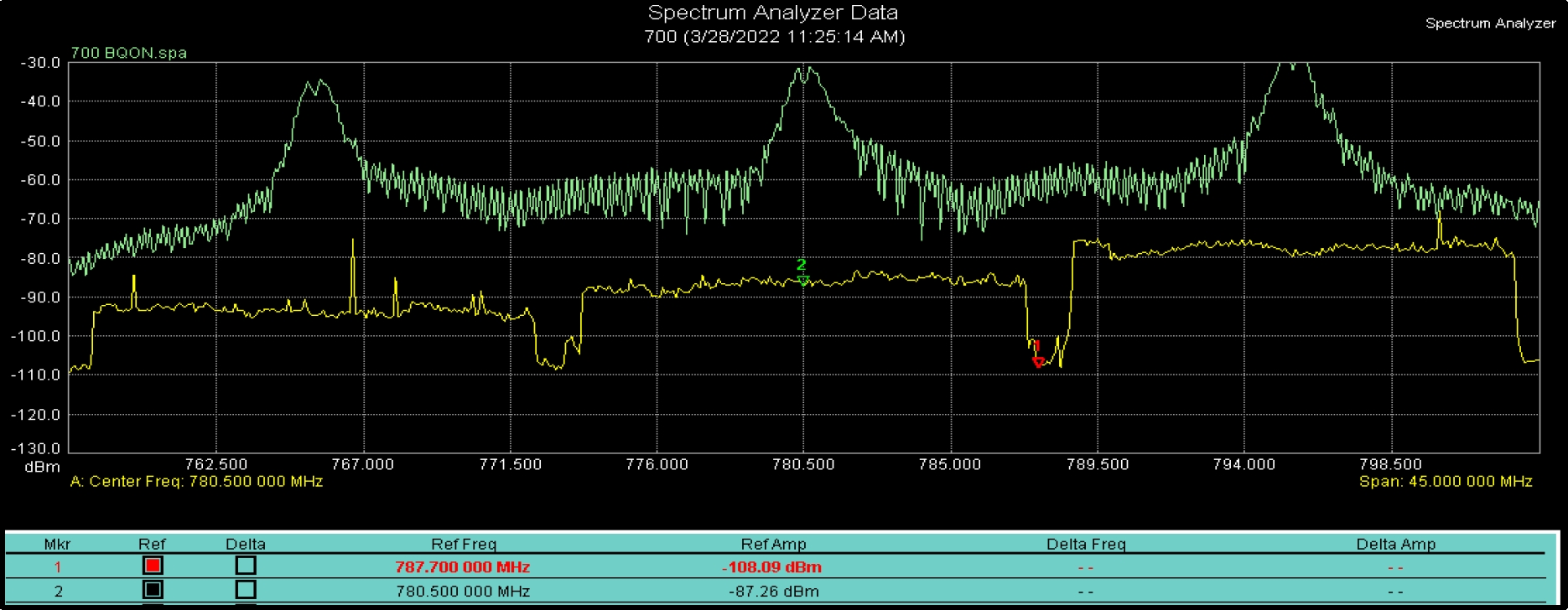
As a reference, one can resort to the theoretical study where an LTE signal (2.6 GHz) of 5 MHz RF width is blocked with a jamming signal of 465 KHz, according to the study [12], attached as a practical example is the blocking of an LTE signal 700 MHz, 15 MHz RF width, with a jamming signal of 2 MHz, according to Figure 6 and Figure 7.
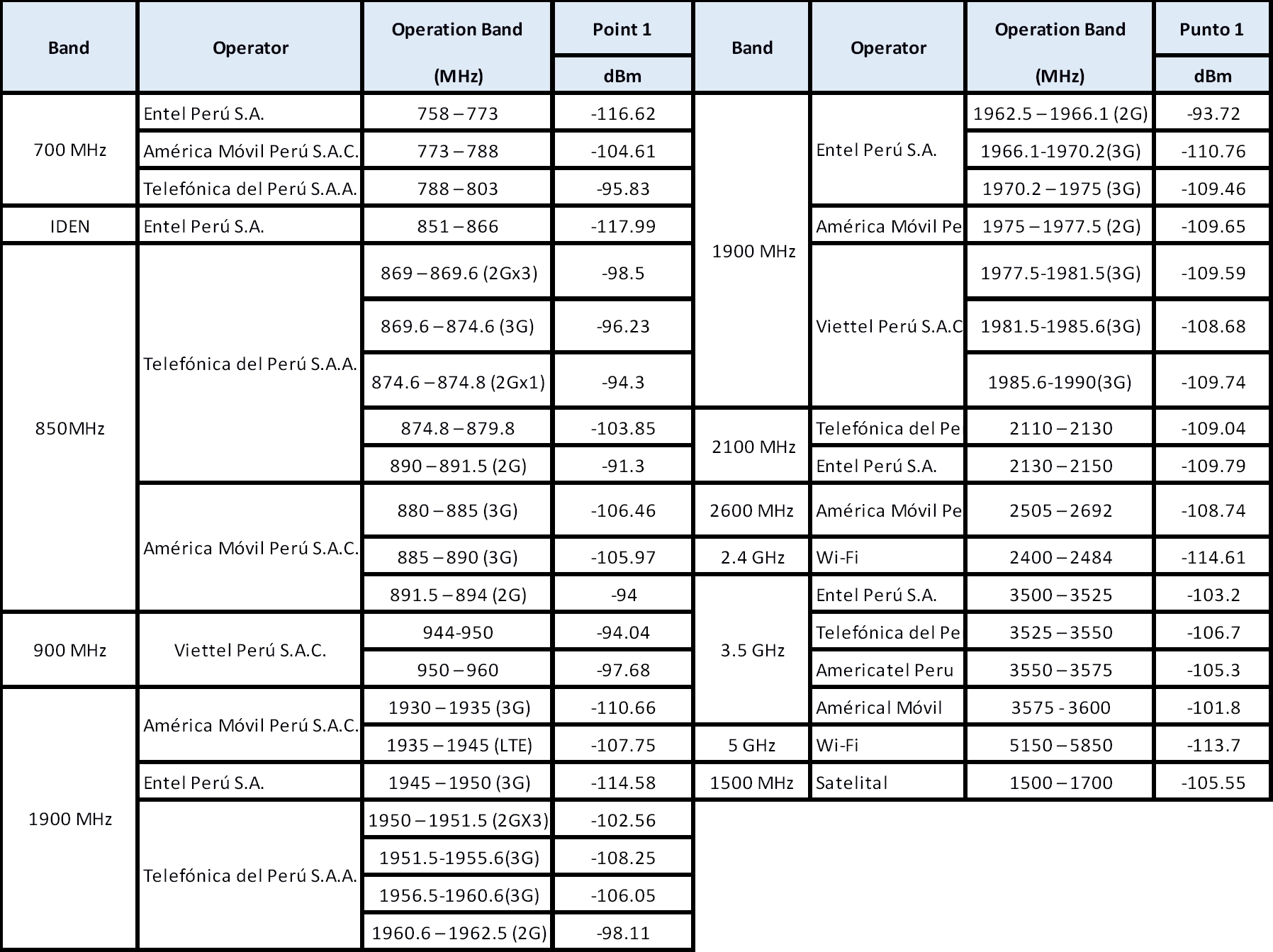
Additionally, as shown in Figure 8, an example of the hardware required to be installed on the antennas of the blockers to minimize propagation to the nearby population is presented. Also, specific operating frequencies for blocking public telecommunications services in penal establishments are available, usually blocking on the Down Link, as indicated in Table 2.
4.4 Phase 4: Execution
Exhaustive research has been conducted to ensure that the implementation of the infrastructure does not have adverse impacts on the surrounding population or cause interference with mobile operators' services. Subsequently, the installation of such infrastructure in penal facilities progresses, adhering to the meticulously outlined guidelines in the specialized technical studies.
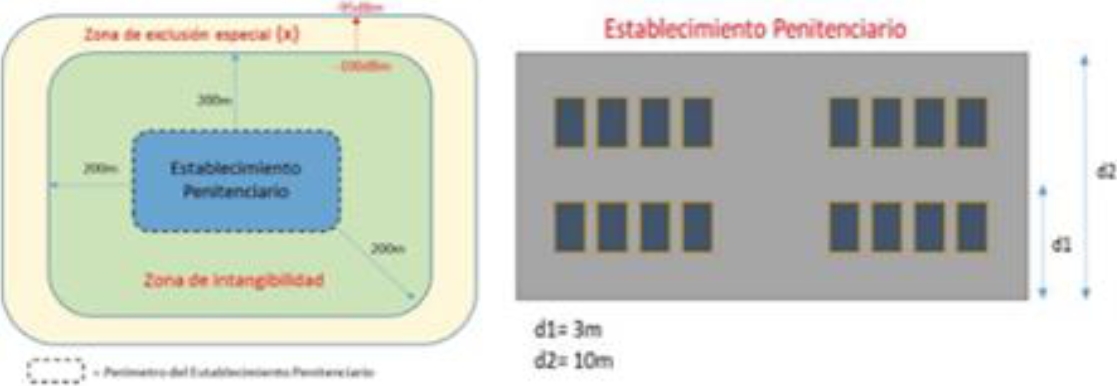
These studies include analysis on the non-affectation to the community and the absence of interference with mobile operators, culminating in the production of illustrated deliverables, as shown in Figure 9. Afterward, the installation of all the infrastructure mentioned in Phases 2 and 3 was verified. Once the conformity of the installation of all the technological infrastructure was confirmed, the Equipment Installation Act of the respective penal establishment will be signed, as well as the following tests:
− The blocking within the penal establishment.
− The non-affectation to the population within a distance of 200 meters from the perimeter of the penal establishments, defined as an untouchability zone, of the public telecommunications services.
− The non-interference with mobile operators, which involves measurements beyond 200 meters.
During this critical phase of the process, it's important to note that multiple instances of feedback from other stages or phases within the FRS methodology may emerge. This is due to the performance of essential calibrations aimed at achieving the pre-established objectives.
Consequently, various adjustments may be needed to ensure the achievement of the defined goals. MINJUS sector experts will be responsible for conducting technical evaluations following their established protocol to verify the effectiveness of signal blocking within the penitentiary facility:
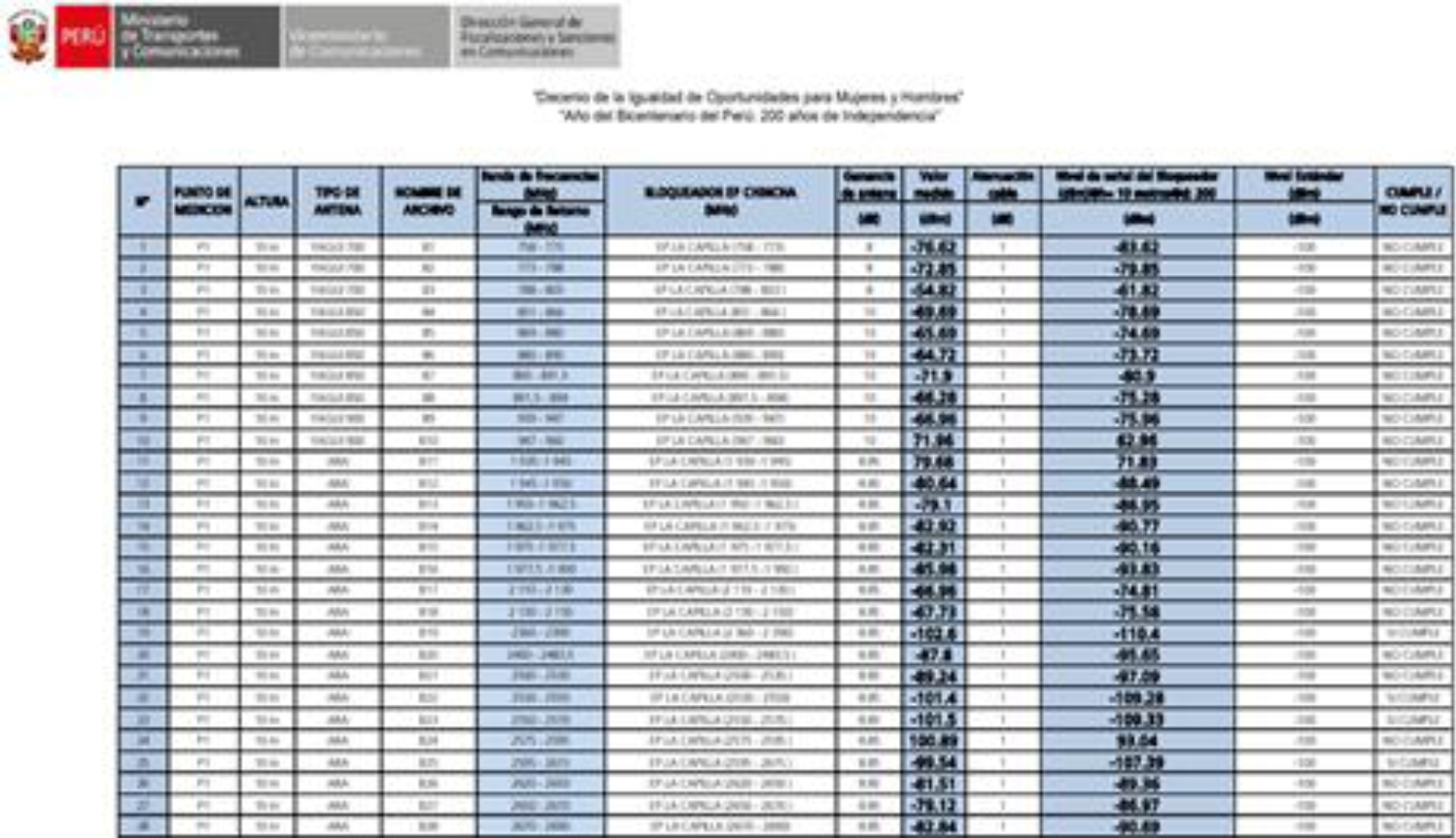
4.5 Phase 5: Verification
Specialized personnel from the Ministry of Transport and Communications (MTC) will conduct verifications to determine if there are impacts on public telecommunications services in the untouchability zone due to the blocking system, as well as interference with mobile operators. These verifications are carried out in accordance with R.M. 954-2016-MTC/01.03. If the results of the verifications are favorable, that is, no impacts are detected, the corresponding operation permits will be granted. In this phase, the following tests are performed: Verify if the blocking systems emit signals outside the range of Downlink frequencies, including all the blocking frequency bands.
Special attention is paid to the possibility that these signals are emitted in the Uplink range, which could indicate that the noise generated beyond the Downlink range has a reach that exceeds the untouchability zone, which is usually located more than 200 meters away.
The purpose of this verification is to assess the possibility of negative interference occurring at the base stations (BTS) of mobile operators, which can result in deliverables shown in Figure 10. MTC's specialized personnel determine if there is a significant impact on public telecommunications services in the areas surrounding the penal establishments, up to 200 meters from the untouchability zone. The main goal is to ensure that the population is served by any mobile operator or internet service provider.
The tests are performed following the Technical Protocol established in Ministerial Resolution 954-2016-MTC/01.03 by the MTC, as seen in Figure 11. The MTC, within the framework of its tests, generates technical reports that include the following reports, as seen in Figure 12.
After conducting the tests, and if it cannot be confirmed that there are no impacts on public telecommunications services in the untouchability zone around the prisons, and there are no interferences with mobile operators, the specialized personnel from MINJUS will proceed to perform initial measurements of the radiofrequency (RF) signals.
This will allow for obtaining an "initial snapshot" of the situation of the RF levels of mobile operators operating within the prisons. Additionally, the MINJUS sector will create the corresponding reports to approve the start of operations of the blocking systems in the respective prison. The authorization to start operations is essentially a letter to the Provider, Prisontec S.A.C.
The initial snapshot, generated by the specialized MINJUS personnel, is the deliverable shown in Figure 13.
4.6 Phase 6: Monitoring and Control
After completing all the test phases, performing the relevant verifications, and obtaining the necessary authorizations, this stage, which spans from the start of operations to the end of the contract, will mark the beginning of the full operability of the blocking systems. These systems will be subject to constant monitoring, carried out by both specialized personnel from MINJUS and MTC.
This meticulous monitoring will cover the management and control of the blocking system within the penal facilities, as well as the analysis of possible impacts on public telecommunications services and interferences to the base stations of mobile operators located in the vicinity of the penal establishments.
5 Results and Discussion
This section presents the results obtained from the implementation of the FRS methodology in penal establishments and discusses these results in detail. The effects of applying Best Practices on radio-electronic signal blocking systems and their impact on the systems' efficiency, as well as on mitigating negative impacts on the population and mobile operators, are examined.
Additionally, RF signal measurements are analyzed, and it is evaluated whether the blocking systems comply with regulations to avoid generating interferences at mobile operators’ base stations.
5.1 Results
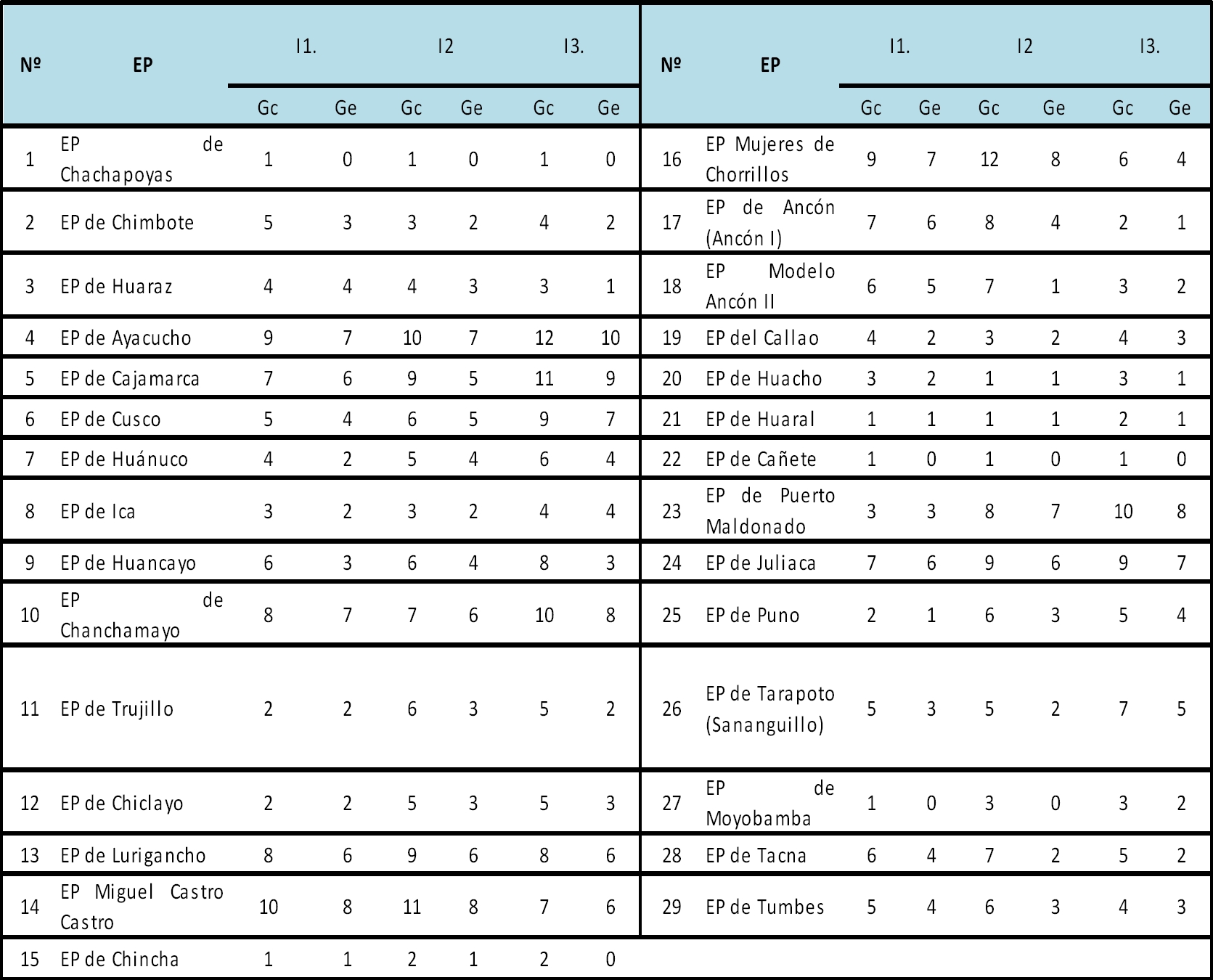
Following the implementation of the proposed solution, specific values have been recorded for the following indicators: Number of Events of failures in the blocking of the EPs, Number of requests to the MTC for measurements, and Number of social protests in the vicinity of the EP.
5.2 Experimental Results: Reduction of I1, I2, and I3
30 values for each indicator were collected using various statistical techniques, the results of which are detailed in Figure 14. This data collection provides a broad and detailed view of the performance and implications of the implemented measures, allowing for a rigorous evaluation of their effectiveness in the studied context.
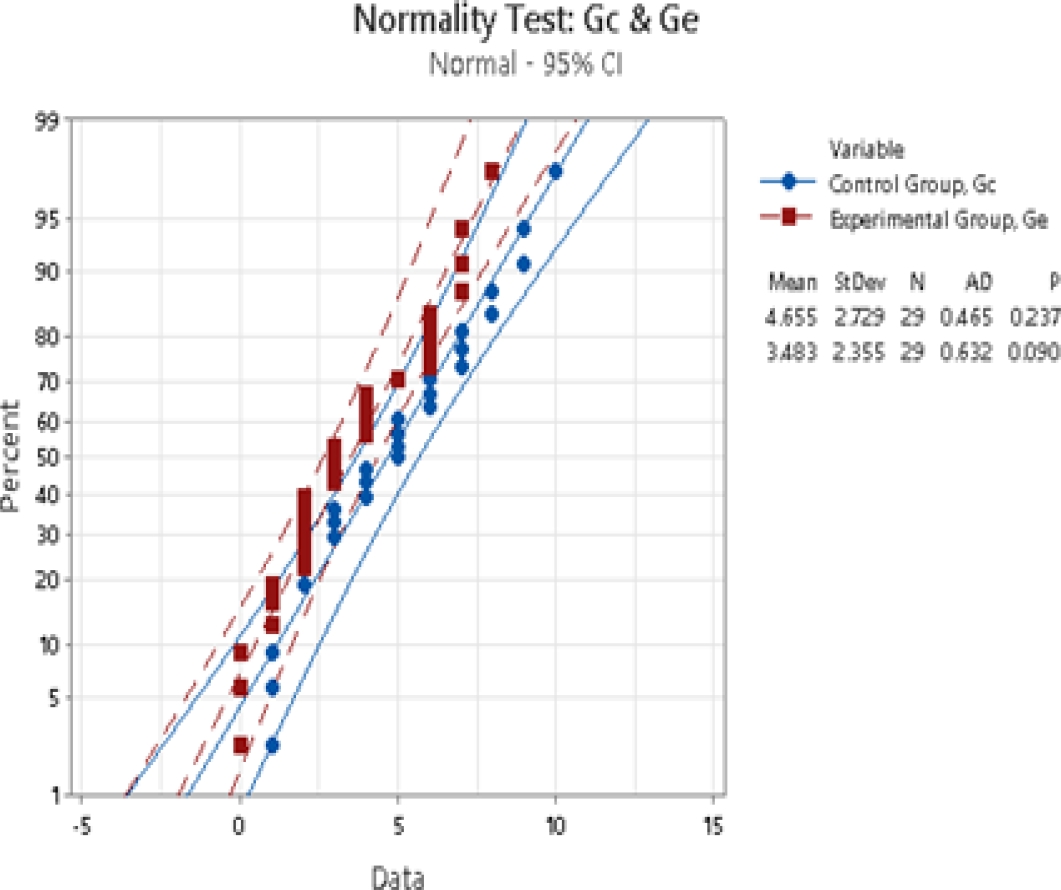
5.3 Normality Test
This test focuses on comparing the Empirical Cumulative Distribution Function (ECDF) derived from the sample data and the theoretical distribution expected under the assumption of normality.
The evaluation is performed for three key indicators, providing a quantitative measure of how well the observed data fit a normal distribution model. (See Figure 15, Figure 16, and Figure 17).
I1: Number of Event Failures in the Blocking at Penal Establishments (EPs)
For this indicator I1, in the tests for the control group (Gc) and the experimental group (Ge), the results are: 0.237 and 0.090, respectively, both are >
I2: Number of Requests to the MTC for Measurements
For this indicator I2, in the tests for the control group (Gc) and the experimental group (Ge), the results are: 0.475 and 0.117, respectively, both are >
I3: Number of Social Protests in the Vicinity of the EPs
For this indicator, in the tests for the control group (Gc) and the experimental group (Ge), the results are: 0.161 and 0.052, respectively, both are >
5.4 Discussion of the Results
The discussion is carried out with a critical and honest approach by the researchers, who commit to respecting the integrity of the original results. This involves an ethical commitment not to alter or distort the information obtained during the research.
5.4.1 With Descriptive Statistics
A preliminary analysis of the data is conducted, facilitating the identification of defined patterns within the collected information set. The specific details of this analysis are presented in Table 3 and Table 4. According to the results obtained from the Anderson-Darling normality test, both the AD value and the p-value turned out to be greater than the significance level α (0.05); therefore, the normality of the analyzed data is confirmed.
This indicates that, with a 95% confidence level, both the mean and the standard deviation of the data corresponding to the indicators reflect a normal distribution. This finding is fundamental for the use of parametric statistical techniques in subsequent analyses.
For each indicator presented in the table, it is observed that approximately 95% of the values are within a range of up to two standard deviations from the mean, suggesting a consistent and predictable data distribution. The kurtosis, indicating low peaks, suggests that the distribution is relatively flat, implying fewer extreme values.
On the other hand, the skewness towards lower values indicates that most of the data cluster on the lower side of the scale, and the third quartile (Q3) reveals that 75% of the values are less than or equal to this specific point.
For Indicator 1, the quantity of complaints about failures is how the efficiency of the blocking systems is evaluated. Regarding the efficiency of jamming equipment with 4G LTE radio-electronic signals of mobile operators, the work by Mert Eygi and Gunes Karabulut Kurt [4] indicates that if the synchronization signals for LTE follow the specifications of the 3GPP standard, in the subframe from 0 to 5, high levels of blocking efficiency are achieved.
The study by Mohamed Samir Elatif Soliman [7] has shown that partial band interference is more effective at the center where the synchronization channels and PBCH are located, managing to reduce the Bit Error Rate (BER) of 4G LTE signals to values of 0.5 and 0.22, when the standard value is 10 E-06.
Furthermore, according to the studies by Ali Abubakar et al. [9], the results of the most effective interference waveform and simulation results show a Packet Error Rate (PER) of 100% when employing Gaussian noise waveforms and modulated QPSK.
In addition, in the study by Triet Vo-Huu et al. [10], a new interference strategy with the IEEE 802.11 interleaving mechanism is developed to actively introduce burst errors in the Wi-Fi receiver, which can destroy more than 95% of the transmitted packets by using an interference power equivalent to only 0.1% of the normal transmitted signal power.
When the interference power increases to a fraction of 1%, this strategy can completely block all packets. Also, Samir and Shaheen [2] mention various blocking signal models, but it was shown that the proposed waveform interference technique completely deteriorates the BER performance of the OFDM system, which increases blocking efficiency and reduces the possibility of events and complaints of failures.
The application of the radio-electronic signal blocking scheme transcends its primary use in penal establishments, leading to its implementation in various contexts that require strict communication control to preserve integrity and security.
A notable implication of this approach is its potential application in university entrance exams, as well as in police and military training institutions, where it is critical to prevent fraud and ensure fairness. Similarly, the scheme emerges as a valuable tool for security in the banking sector, where signal blocking can prevent the misuse of electronic devices for illicit purposes.
For Indicator 2, the quantity of requests to the MTC to perform RF signal measurements is related to the intervention of the entity managing the radio-electric spectrum to regulate the activity of blockers as well as mobile operators around the prisons. Regarding RF signal measurement, the study by Oluyomi Simpson and Yuchuang Sun [35], who perform measurements of LTE signal received and measured from a base station (EBC) operating in the 2100 MHz band with a height of 15 m, a Tx power of 58.7 dBm and 2100 MHz, measured the following parameters:
Reference Signal Received Power (RSRP) in dBm, Reference Signal Received Quality (RSRQ) in dB, and Reference Signal Signal to Noise Ratio (RSSNR) in dB, with statistical values such as mean, standard error, median, mode, standard deviation, variance, kurtosis, etc.
According to the study by José Martínez Morales and Alvaro Casallas Hernández [36], in the Analysis of the Normative Impact of the National Spectrum Agency (ANE) and the Ministry of Information and Communication Technologies (MinTIC), who made adjustments to the blockers and despite the adjustments made by mobile operators, the National Penitentiary Institute of Colombia (INPEC) stated that there is still a need to implement more robust technical measures that lead to attenuating as much as possible the emissions coming from the base stations within the prisons, to ensure the success of the radio-electric signal inhibition.
According to the study by Hsing-Yi and Tsung-Han Lin [37], using the Finite Difference Time Domain (FDTD) method is used to perform measurements simulating radiation patterns of an LTE base station antenna in vertical and horizontal planes at frequencies of 1795, 1920, and 2060 MHz respectively.
Also, according to the research conducted by Mahendra, Budiman, Cahyadi, and Taruk [1], the best deviation from Telkomsel operators is -64 dBm and the worst is -114 dBm.
The best point for XL operator is -69 dBm, the worst is -101 dBm, and for the best point of IM3 operator is -64 dBm, the worst is -104 dBm. According to Pramono, Alvionita, and Eko [38], the optimal levels for receiving LTE signal are: good (-80 to -90dBm), fair (-90 to -100 dBm), and poor (-100 to -110 dBm), expressed in RSRP (Reference Signal Reception Power) which is the amount of signal from the LTE station.
It is crucial to highlight the application of the FRS methodology as a significant implication both in the supervision of the current contract for the installation of blockers and in telecommunications projects in rural areas.
This methodology not only facilitates the effective implementation of signal blocking systems in penal environments but also promotes their use in the development of telecommunications infrastructure in less accessible areas, contributing to reducing the digital divide.
Additionally, the FRS methodology proves instrumental in determining optimal signal levels in the vicinity of prisons, ensuring that current legal regulations are effectively complied with.
For Indicator 3, the quantity of social protests or conflicts around the prisons, according to the study by Juan Pablo Parra and Carolina Botero [39], concludes that it is necessary for the State to create an independent mechanism that periodically reports the state of telecommunications to allow public scrutiny of internet quality and access.
They also recommend the State commit to not using signal jammers as much as possible with a policy respectful of rights, as well as requesting mobile operators (internet) in exercising their responsibility to users to analyze every request for blocking or interference.
The entity managing the radio-electric spectrum must investigate complaints about signal interference and internet access to protect citizens' rights.
In this line, the study by José Martínez Morales and Alvaro Casallas Hernández [36], in the Analysis of the Normative Impact of the National Spectrum Agency (ANE) and the Ministry of Information and Communication Technologies (MinTIC), pointed out complaints from citizens about failures in mobile communication services, and for this reason, some citizens have activated judicial mechanisms to seek to protect the fundamental right to communication, having as a sentence in some cases the order to INPEC, the shutdown of the signal inhibition systems.
Also, in the study by Juan Cueva Silva and Giovane Mendieta Izquierdo [40], the social protest in Latin America in 2019 is not the same as in the early years of the new millennium or before, in the midst of this information and communication revolution, the interference of social networks in the dissemination of information is evidenced, with the use of the various services provided by the Internet, with the publication of videos and chats, as well as the manifestation of positions through Twitter, Facebook, and Instagram, without forgetting the chains in WhatsApp, has become the protagonist of a social protest that gets out of the hands of failed democratic systems and traditional media.
According to Pozo León [41], the installation of blockers in Ayacucho has experienced a loss in mobile communications and Wi-Fi in the population surrounding the prison, even its impact was greater during the COVID-19 pandemic, affecting virtual classes and remote work, which constitutes a negative impact, this research evidences the origin of the social protests that occurred in the place, as well as other places in the country.
In contrast, according to Villamizar and Sorzano [42], there was a belief that mobile phone antennas could produce lethal damage and that it was related to the spread of covid-19. Speculation and rumors about this relationship led to social mobilization and the demand for the dismantling of the antenna.
Finally, the application can be extended to the management of social conflicts derived from infrastructure and the provision of public goods and services.
Through the implementation of the FRS methodology, it is possible to effectively monitor the possible effects on the population, including not only public telecommunications services but also other essential public services that may be impacted.
This approach allows addressing the community's concerns and needs proactively, ensuring that the implemented measures not only meet technical and security objectives but also minimize the negative impact on citizens' quality of life.
5.4.2 With Inferential Statistics
In Table 5, the results derived from the application of statistical tests are presented, which have been used to effectively contrast the proposed hypotheses. These values are crucial for determining the validity of the hypotheses and, therefore, to support the conclusions of the research. Since all p-value results are less than α (0.05), the results provide evidence to reject the null hypothesis (Ho), and the alternative hypotheses were true, making the tests significant.
6 Conclusions and Future Research
The findings of this study lead to several conclusions. Firstly, it has been demonstrated that the use of Best Practices applying the FRS methodology decreases the number of events or complaints about failures in blocking, meaning it will increase the efficiency of the Radio-Electronic Signal Blocking System in Penal Establishments.
Another result of this study confirms that the use of Best Practices applying the FRS methodology reduces the number of requests to the MTC for signal measurements to detect signal levels above what is permitted, in areas near where the Radio-Electronic Signal Blocking System is installed in Penal Establishments.
Finally, one of the outcomes of this study is the reduction in the number of social protests in populations near the prisons, which occur due to the negative impact on public Telecommunications services, where the Radio-Electronic Signal Blocking Systems are managed.
A limitation of this study is not having reduced the events of failures to a greater extent. For future work, the study should include blocking of 5G NSA technology at an experimental level, as it has not yet been fully deployed for 5G NSA technology.
Also, the formation of an online monitoring system of the signals emitted by both mobile operators and blockers is suggested.











 nueva página del texto (beta)
nueva página del texto (beta)